Data Destruction services
About Data Destruction Services
Data destruction services, a critical aspect of information security, involve deleting or permanently erasing data stored on various electronic devices to prevent unauthorized access or retrieval. In today's digital age, where data breaches pose significant threats to individuals and organizations, ensuring the secure destruction of sensitive information is of paramount importance.
Rapid Solutions International is a leading provider of data destruction services, offering various methods of data destruction for different types of data-bearing devices or media, such as hard drives, media drives, SD cards, and cell phones. Whether on-site or off-site, we perform data destruction with the highest level of security, transparency, and efficiency, while providing value-added services such as asset serialization, destruction witnessing, IT Asset Disposition (ITAD), and more.
The data destruction process involves a variety of methods, each designed to meet specific security requirements and compliance standards. The most common methods are physical destruction, data erasure, degaussing, and encryption.
Additionally, we use a robust reporting and services management portal that delivers real-time visibility and tracking of material, as well as documentation and certification of data destruction. By following the R2v3 standard, the highest certification available in the field of data destruction, we ensure compliance with environmental, health, and safety regulations.
Our Data Destruction Services
Data destruction plays an important role in safeguarding sensitive information and mitigating the risks associated with data breaches. By employing suitable records destruction strategies and adhering to regulatory requirements, agencies can uphold information security standards, protect patron privacy, and preserve trust and credibility in a modern digital landscape. Some of the information destruction strategies that Rapid Solutions International gives are:
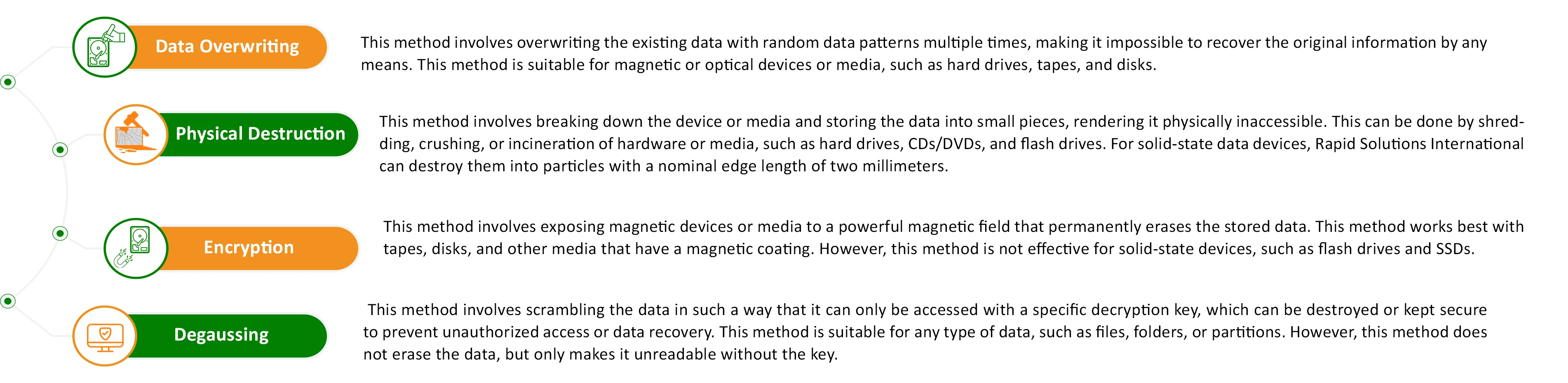 These strategies may be used individually or in aggregate, relying on the safety requirements and compliance requirements of the organization. Each method has its blessings and obstacles, and the selection of approach may additionally vary based on factors which include the kind of information, the storage media involved, and the extent of security required.
These strategies may be used individually or in aggregate, relying on the safety requirements and compliance requirements of the organization. Each method has its blessings and obstacles, and the selection of approach may additionally vary based on factors which include the kind of information, the storage media involved, and the extent of security required.
Why Choose Data Destruction Services
- Data Security: Data destruction includes the everlasting elimination of touchy and old data, making sure that confidential data is blanketed and inaccessible to unauthorized people.
Compliance with Regulations: Businesses are required to comply with facts safety rules which include GDPR in Europe and CCPA within the United States. Data destruction offerings assist businesses adhere to these policies by securely casting off facts in keeping with criminal requirements.
Privacy Preservation: One of the number one benefits of data destruction is the renovation of consumer privacy and sensitive facts. It demonstrates a business's dedication to responsibly safeguarding consumer statistics.
Improved Efficiency: By disposing of out-of-date and pointless records, enterprise databases and structures emerge as cleaner and greater streamlined. This can result in progressed inner and external overall performance, reducing gadget glitches and errors.
Cost Savings: Data destruction reduces costs associated with statistics storage and control. This price-powerful degree can increase enterprise profitability by saving on needless costs.
Social Responsibility: Employing environmentally friendly information destruction techniques contributes to lowering environmental pollution and enhancing environmental conditions. It reflects an enterprise's commitment to social responsibility and environmental stewardship.
Enhanced Customer Trust: Providing first-class and secure data destruction services enhances customer trust and satisfaction. It can make contributions to improving the popularity and success of the enterprise, including similar costs to the purchaser experience and strengthening positive patron relationships.
Secure Data Destruction: Rapid Solutions Leading the Way
Rapid Solutions offers enhanced security for sensitive information through cutting-edge data destruction methods and certifications, ensuring complete protection against unauthorized access. With internationally recognized credentials such as ISO 27001 and R2v3, the company stands out as a leader in IT asset disposal and data eradication, guaranteeing compliance with stringent regulatory standards. Tailored to individual requirements, Rapid Solutions provides personalized data destruction solutions, prioritizing customer privacy and confidentiality. Backed by nearly a decade of experience, the company delivers reliable expertise, cost-effective services, and environmentally responsible practices, ensuring customer satisfaction and peace of mind.
We offer robust data destruction services designed to securely and efficiently erase all sensitive information from your digital devices. Our services are available throughout the UAE, catering to businesses looking for reliable data destruction services in the UAE.
As a leading data destruction company, we stay ahead in the data destruction service market by adhering to the highest standards and using advanced methods to guarantee complete data eradication and environmental responsibility.
FAQ
Rapid Solutions International offers various data destruction methods to meet specific security and compliance requirements. These methods include physical destruction, data erasure, degaussing, and encryption. Each method is designed to securely eliminate data from different types of data-bearing devices such as hard drives, media drives, SD cards, and cell phones.
Rapid Solutions International ensures compliance with data protection regulations like GDPR in Europe and CCPA in the United States by securely destroying data according to legal requirements. The company follows the R2v3 standard, the highest certification available in the field of data destruction, and adheres to environmental, health, and safety regulations. Additionally, they provide detailed documentation and certification of data destruction to verify compliance.
Using Rapid Solutions International's data destruction services offers several benefits, including enhanced data security by permanently eliminating sensitive information, compliance with data protection regulations, preservation of privacy, improved efficiency by removing outdated data, cost savings on data storage and management, and demonstrating social responsibility through environmentally friendly practices. These benefits help improve customer trust and satisfaction, enhancing the business's reputation.


.png)
